mirror of
https://github.com/podman-desktop/podman-desktop
synced 2026-04-21 17:47:22 +00:00
fix(docs): remove all linter errors (#7862)
Signed-off-by: Markus Eisele <markus@redhat.com> Co-authored-by: Markus Eisele <markus@redhat.com>
This commit is contained in:
parent
3ea721ade3
commit
37909ac142
20 changed files with 61 additions and 55 deletions
|
|
@ -77,7 +77,7 @@
|
|||
"watch": "node scripts/watch.mjs",
|
||||
"format:check": "prettier --cache --check \"{extensions,packages,tests,types,tools,website-argos}/**/*.{ts,svelte}\" \"extensions/*/scripts/*.{ts,js}\" \"website/**/*.{md,js}\" \"website/src/**/*.{css,tsx}\"",
|
||||
"format:fix": "prettier --cache --write \"{extensions,packages,tests,types,tools,website-argos}/**/*.{ts,svelte}\" \"extensions/*/scripts/*.{ts,js}\" \"website/**/*.{md,js}\" \"website/src/**/*.{css,tsx}\"",
|
||||
"markdownlint:check": "markdownlint-cli2 \"website/**/*.md\" \"#website/node_modules\"",
|
||||
"markdownlint:check": "markdownlint-cli2 \"website/**/*.md\" \"#website/node_modules\" \"#website/api\"",
|
||||
"markdownlint:fix": "markdownlint-cli2-fix \"website/**/*.md\" \"#website/node_modules\"",
|
||||
"lint:clean": "rimraf .eslintcache",
|
||||
"lint:fix": "node --max-old-space-size=6144 node_modules/eslint/bin/eslint.js --cache . --fix --ext js,ts,tsx,svelte",
|
||||
|
|
|
|||
|
|
@ -17,7 +17,7 @@ The challenges are to run a desktop tool (Podman Desktop) and running a containe
|
|||
|
||||
## Defining image of the container
|
||||
|
||||
The first thing is in the choice of the image for the container. It is possible to pick-up a default image and add some features but there is no existing feature for Podman at https://github.com/devcontainers/features/tree/main/src and most of the features are expecting to run on top of Debian/Ubuntu
|
||||
The first thing is in the choice of the image for the container. It is possible to pick-up a default image and add some features but there is no existing feature for Podman at [https://github.com/devcontainers/features/tree/main/src](https://github.com/devcontainers/features/tree/main/src) and most of the features are expecting to run on top of Debian/Ubuntu
|
||||
|
||||
If you are not interested in how to setup the image, jump to the [next section](#configure-the-devcontainer-using-devcontainerjson).
|
||||
|
||||
|
|
@ -31,6 +31,8 @@ FROM quay.io/fedora/fedora:37
|
|||
|
||||
Then I install Node.js 16 from official nodejs.org repository. It's easier to switch to the version that we need.
|
||||
|
||||
<!-- markdownlint-disable MD034 -->
|
||||
|
||||
```docker
|
||||
# install Node.js + yarn
|
||||
ENV NODE_VERSION 16.18.1
|
||||
|
|
|
|||
|
|
@ -44,7 +44,7 @@ Certain VPN setups or other specialized networking configs will block traffic fr
|
|||
|
||||
|
||||
|
||||
### Compose group Summary tab [#3317](https://github.com/containers/podman-desktop/pull/3317),
|
||||
### Compose group Summary tab [#3317](https://github.com/containers/podman-desktop/pull/3317)
|
||||
|
||||
Compose group Summary tab shows all containers in the group and let you navigate to Details page for specific container.
|
||||
|
||||
|
|
|
|||
|
|
@ -159,7 +159,7 @@ The 🦭 Podman Desktop extension API received many improvements, including:
|
|||
|
||||
- An issue with incorrect terminal behavior in response to long lines in the terminal attached to a container has been resolved. [#3955](https://github.com/containers/podman-desktop/pull/3955)
|
||||
|
||||
- A spacing issue on the run image form has been corrected. [#4089]https://github.com/containers/podman-desktop/pull/4089
|
||||
- A spacing issue on the run image form has been corrected. [#4089](https://github.com/containers/podman-desktop/pull/4089)
|
||||
|
||||
- The "podify" icon & button on the Containers list was unusually large in release 1.4. That regression has been corrected in this release. [#4122](https://github.com/containers/podman-desktop/pull/4122)
|
||||
|
||||
|
|
|
|||
|
|
@ -27,7 +27,7 @@ In this blog post, we will explore the best practice for streamlining the image
|
|||
|
||||
When using kind or minikube or other 3rd party tools to setup a local kubernetes cluster, we have several ways to publish images.
|
||||
|
||||
Minikube published 8 ways of doing that at https://minikube.sigs.k8s.io/docs/handbook/pushing/
|
||||
Minikube published 8 ways of doing that at [https://minikube.sigs.k8s.io/docs/handbook/pushing/](https://minikube.sigs.k8s.io/docs/handbook/pushing/)
|
||||
|
||||
There are pros and cons either way. Using a third party registry implies that you need to publish the image after each build of the image before being able to use it in the kubernetes cluster. While Podman Desktop could automate the synchronization between the local registry (where you are doing `podman build`) and the third party registry, there remains a duplication of layers between the local and third party registry. And if you change the first layer, it can take a lot of time to send again all the data.
|
||||
|
||||
|
|
@ -44,11 +44,11 @@ Could we just build the image and use it in kubernetes?
|
|||
In the kubernetes world, we need a container engine runtime. At the early stage, container runtimes were integrated with ad hoc solutions on top of docker, rkt, or others.
|
||||
|
||||
But to separate concerns and to be extensible, a new interface was added: CRI for "Container Runtime Interface". Using the CRI interface we can plug container engines. And there are several runtimes such as containerd, cri-o and others.
|
||||
https://github.com/kubernetes/community/blob/master/contributors/devel/sig-node/container-runtime-interface.md
|
||||
[https://github.com/kubernetes/community/blob/master/contributors/devel/sig-node/container-runtime-interface.md](https://github.com/kubernetes/community/blob/master/contributors/devel/sig-node/container-runtime-interface.md)
|
||||
|
||||
What is interesting to us is the cri-o project. This project is implementing the CRI interface but also adopting some projects of the [containers](https://github.com/containers) organization where [podman](https://github.com/containers/podman) and [podman-desktop](https://github.com/containers/podman-desktop) live.
|
||||
|
||||
So it means cri-o uses image management from https://github.com/containers/image project and handle storage with https://github.com/containers/storage project.
|
||||
So it means cri-o uses image management from [https://github.com/containers/image](https://github.com/containers/image) project and handle storage with [https://github.com/containers/storage](https://github.com/containers/storage) project.
|
||||
|
||||
And this is what is really interesting as a podman user. As it is using common libraries between cri-o and podman, it means that in the same environment, podman and cri-o read and write the images at a common location in `/var/lib/containers` folder.
|
||||
|
||||
|
|
@ -62,9 +62,9 @@ While we have the goal of using both cri-o and podman altogether, we can explore
|
|||
|
||||
### kind
|
||||
|
||||
On the `kind` side, there is a default configuration that is using containerd and there is no plan to support an alternative such as cri-o https://github.com/kubernetes-sigs/kind/issues/1369#issuecomment-867440704
|
||||
On the `kind` side, there is a default configuration that is using containerd and there is no plan to support an alternative such as cri-o [https://github.com/kubernetes-sigs/kind/issues/1369#issuecomment-867440704](https://github.com/kubernetes-sigs/kind/issues/1369#issuecomment-867440704)
|
||||
|
||||
That said, some people try to maintain a way to do that but not officialy https://gist.github.com/aojea/bd1fb766302779b77b8f68fa0a81c0f2
|
||||
That said, some people try to maintain a way to do that but not officialy [https://gist.github.com/aojea/bd1fb766302779b77b8f68fa0a81c0f2](https://gist.github.com/aojea/bd1fb766302779b77b8f68fa0a81c0f2)
|
||||
|
||||
By doing that, we would also need to mount `/var/lib/containers` folder from the host (the podman machine) to the container. And there is no easy flag in kind.
|
||||
|
||||
|
|
@ -97,7 +97,7 @@ Regarding the configuration of cri-o, currently, it's not achievable using Minik
|
|||
Let's do our own base image named kicbase image.
|
||||
|
||||
Minikube includes a default configuration file for cri-o.
|
||||
https://github.com/kubernetes/minikube/blob/v1.32.0/deploy/kicbase/02-crio.conf
|
||||
[https://github.com/kubernetes/minikube/blob/v1.32.0/deploy/kicbase/02-crio.conf](https://github.com/kubernetes/minikube/blob/v1.32.0/deploy/kicbase/02-crio.conf)
|
||||
|
||||
We need to change this default configuration to say that for storing the images, cri-o needs to use another directory. This new directory `/host-containers` will be mounted from the `/var/lib/containers` folder inside the podman machine. This is how cri-o is able to see podman images.
|
||||
|
||||
|
|
@ -111,7 +111,7 @@ runroot = "/host-containers/storage"
|
|||
|
||||
Let's also upgrade the Podman inside the container by adding the necessary instruction to the Dockerfile.
|
||||
|
||||
The Dockerfile is coming from https://github.com/kubernetes/minikube/blob/v1.32.0/deploy/kicbase/Dockerfile#L178-L186
|
||||
The Dockerfile is coming from [https://github.com/kubernetes/minikube/blob/v1.32.0/deploy/kicbase/Dockerfile#L178-L186](https://github.com/kubernetes/minikube/blob/v1.32.0/deploy/kicbase/Dockerfile#L178-L186)
|
||||
|
||||
In the file, replace
|
||||
|
||||
|
|
@ -121,6 +121,8 @@ RUN clean-install podman && \
|
|||
|
||||
with
|
||||
|
||||
<!-- markdownlint-disable MD001 MD034 -->
|
||||
|
||||
```Dockerfile
|
||||
RUN sh -c "echo 'deb https://downloadcontent.opensuse.org/repositories/devel:/kubic:/libcontainers:/unstable/xUbuntu_22.04/ /' > /etc/apt/sources.list.d/devel:kubic:libcontainers:unstable.list" && \
|
||||
curl -LO https://downloadcontent.opensuse.org/repositories/devel:kubic:libcontainers:unstable/xUbuntu_22.04/Release.key && \
|
||||
|
|
@ -131,7 +133,7 @@ RUN sh -c "echo 'deb https://downloadcontent.opensuse.org/repositories/devel:/ku
|
|||
```
|
||||
|
||||
Let's rebuild the image and publish it. You can find it at `quay.io/fbenoit/kicbase:multiarch-2023-11-06` .
|
||||
To build the image, clone https://github.com/kubernetes/minikube repository, and edit the files referenced before.
|
||||
To build the image, clone [https://github.com/kubernetes/minikube](https://github.com/kubernetes/minikube) repository, and edit the files referenced before.
|
||||
|
||||
The command to build the kicbase image is `make local-kicbase`.
|
||||
|
||||
|
|
@ -151,6 +153,8 @@ Ok now let's try in two steps:
|
|||
podman machine init --cpus 4 --memory 6000 --rootful
|
||||
```
|
||||
|
||||
<!-- markdownlint-disable-next-line -->
|
||||
|
||||
2. Start the cluster using our kicbase image
|
||||
|
||||
We specify Podman as the driver (the default is Docker), state our preference to use cri-o as the container runtime instead of containerd, use our custom image that performs the update of Podman's version and the modification of cri-o's configuration to use a different storage folder. Finally, we specify an additional mount.
|
||||
|
|
@ -177,7 +181,7 @@ kubectl get pods -l app=nginx
|
|||
|
||||
and if you check your podman images
|
||||
|
||||
```
|
||||
```shell
|
||||
podman images
|
||||
```
|
||||
|
||||
|
|
|
|||
|
|
@ -218,7 +218,7 @@ Coming with this new version of 🦭 Podman Desktop, the documentation has been
|
|||
🎉 We’d like to say a big thank you to everyone who helped to make 🦭 Podman Desktop even better. In this
|
||||
release we received pull requests from the following people:
|
||||
|
||||
- [afbjorklund](https://github.com/afbjorklund) in [fix: add website target for running vale ](https://github.com/containers/podman-desktop/pull/4547), [docs: the main lima command is limactl](https://github.com/containers/podman-desktop/pull/4623), [ docs: lima provider cleanup after the merge](https://github.com/containers/podman-desktop/pull/4622), [docs: make it possible for lima to provide both](https://github.com/containers/podman-desktop/pull/4789), [fix: don't link to k8s cluster server](https://github.com/containers/podman-desktop/pull/5087), [feat: show the k8s namespace](https://github.com/containers/podman-desktop/pull/5088), [docs: show location of lima podman socket](https://github.com/containers/podman-desktop/pull/5090)
|
||||
- [afbjorklund](https://github.com/afbjorklund) in [fix: add website target for running vale](https://github.com/containers/podman-desktop/pull/4547), [docs: the main lima command is limactl](https://github.com/containers/podman-desktop/pull/4623), [docs: lima provider cleanup after the merge](https://github.com/containers/podman-desktop/pull/4622), [docs: make it possible for lima to provide both](https://github.com/containers/podman-desktop/pull/4789), [fix: don't link to k8s cluster server](https://github.com/containers/podman-desktop/pull/5087), [feat: show the k8s namespace](https://github.com/containers/podman-desktop/pull/5088), [docs: show location of lima podman socket](https://github.com/containers/podman-desktop/pull/5090)
|
||||
|
||||
- [axel7083](https://github.com/axel7083) in [refactoring: item formats from renderer/preferences in separate files](https://github.com/containers/podman-desktop/pull/3728), [feat: adding optional abort controller to dockerode api](https://github.com/containers/podman-desktop/pull/4364)
|
||||
|
||||
|
|
@ -238,7 +238,7 @@ release we received pull requests from the following people:
|
|||
|
||||
- [EricSmekens](https://github.com/EricSmekens) in [docs: Fixed typo in URI for releases](https://github.com/containers/podman-desktop/pull/4909)
|
||||
|
||||
- [ecrookshanks-rh](https://github.com/ecrookshanks-rh) in [fix: added text beside icon for create pods ](https://github.com/containers/podman-desktop/pull/5095)
|
||||
- [ecrookshanks-rh](https://github.com/ecrookshanks-rh) in [fix: added text beside icon for create pods](https://github.com/containers/podman-desktop/pull/5095)
|
||||
|
||||
---
|
||||
|
||||
|
|
|
|||
|
|
@ -85,13 +85,12 @@ Depending on the output of the command, you might have extra steps to do.
|
|||
|
||||
</TabItem>
|
||||
</Tabs>
|
||||
|
||||
|
||||
### Running Wasm images
|
||||
|
||||
Let's try with a simple hello world sample.
|
||||
|
||||
We will use example coming from https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world
|
||||
We will use example coming from [https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world](https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world)
|
||||
|
||||
There is already an OCI image on quay.io
|
||||
|
||||
|
|
@ -139,7 +138,7 @@ Using this method, we will fetch an image matching our host architecture but as
|
|||
|
||||
Here is a simple Containerfile to build a rust application using wasm32-wasi binary output and a multi-layer OCI image. One layer for the build (installing rust, dependencies and compiling the application) and one scratch layer where we only add the `.wasm` output and flag it as the entrypoint.
|
||||
|
||||
Source code is available at https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world
|
||||
Source code is available at [https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world](https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world)
|
||||
|
||||
`Containerfile` content:
|
||||
|
||||
|
|
@ -215,7 +214,7 @@ Twitter: @Podman_io
|
|||
|
||||
```
|
||||
|
||||
All the source code is available at https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world
|
||||
All the source code is available at [https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world](https://github.com/redhat-developer/podman-desktop-demo/tree/main/wasm/rust-hello-world)
|
||||
|
||||
### Building Wasm images
|
||||
|
||||
|
|
@ -227,7 +226,7 @@ $ podman build --platform=wasi/wasm -t rust-hello-world-wasm .
|
|||
|
||||
example of output will be :
|
||||
|
||||
```
|
||||
```console
|
||||
[1/2] STEP 1/6: FROM docker.io/redhat/ubi9-minimal AS builder
|
||||
Trying to pull docker.io/redhat/ubi9-minimal:latest...
|
||||
Getting image source signatures
|
||||
|
|
@ -298,7 +297,7 @@ $ podman run rust-hello-world-wasm
|
|||
|
||||
and we'll see the expected output
|
||||
|
||||
```
|
||||
```console
|
||||
WARNING: image platform (wasi/wasm/v8) does not match the expected platform (linux/arm64)
|
||||
|
||||
!... Hello Podman Wasm World ...!
|
||||
|
|
|
|||
|
|
@ -18,7 +18,7 @@ We’re honored to announce that [Podman Desktop](https://podman-desktop.io/) ha
|
|||
|
||||
The DEVIES Awards, presented by [DeveloperWeek](https://www.developerweek.com/), recognize the most innovative and impactful tools, platforms, and technologies in the software development community. Podman Desktop's win as the _best innovation in Containers & Kubernetes_ highlights its significant impact on the industry and its role in revolutionizing the way developers build, ship, and run their applications. DEVIES Award winners are selected from hundreds of nominees by the independent, industry-leading DevNetwork Advisory Board.
|
||||
|
||||
## Join us in celebrating!
|
||||
## Join us in celebrating! <!-- markdownlint-disable-line MD026 -->
|
||||
|
||||
We’re excited to be receiving this award on stage at DeveloperWeek 2024, happening on February 21-23, 2024, in Oakland, CA and February 27-29, 2024 (Virtually). In addition, Red Hat developer advocate [Cedric Clyburn](https://github.com/cedricclyburn) will be presenting a session on Podman Desktop, titled “[Going from Containers, to Pods, to Kubernetes – Help for Your Developer Environments!](https://sched.co/1XZ7k)”, with a full presentation on [Podman](https://podman.io/), a demonstration of the Podman Desktop experience, and a multi-tier application going from containers, to pods, to finally Kubernetes!
|
||||
|
||||
|
|
|
|||
|
|
@ -140,7 +140,7 @@ Also we published a test framework to test extensions in separate repositories
|
|||
|
||||
- feat: publish ui components and test component as part of the release [6580](https://github.com/containers/podman-desktop/pull/6580)
|
||||
|
||||
More info on https://github.com/containers/podman-desktop/blob/main/tests/playwright/README.md
|
||||
More info on [https://github.com/containers/podman-desktop/blob/main/tests/playwright/README.md](https://github.com/containers/podman-desktop/blob/main/tests/playwright/README.md)
|
||||
|
||||
---
|
||||
|
||||
|
|
|
|||
|
|
@ -12,7 +12,7 @@ tags: [compose]
|
|||
|
||||
The Compose binary will prioritize the configuration file `~/.docker/config` over Podman credentials.
|
||||
|
||||
### Issues encountered:
|
||||
### Issues encountered
|
||||
|
||||
`docker-credential-desktop` missing:
|
||||
|
||||
|
|
@ -27,6 +27,6 @@ Error response from daemon: {"message":"denied: requested access to the resource
|
|||
Error: executing /usr/local/bin/docker-compose up: exit status 18
|
||||
```
|
||||
|
||||
### Solution:
|
||||
### Solution
|
||||
|
||||
Delete the `~/.docker/config` to clear any errors.
|
||||
|
|
|
|||
|
|
@ -17,7 +17,7 @@ With Podman Desktop, you can manage your container engine workloads.
|
|||
|
||||
#### Procedure
|
||||
|
||||
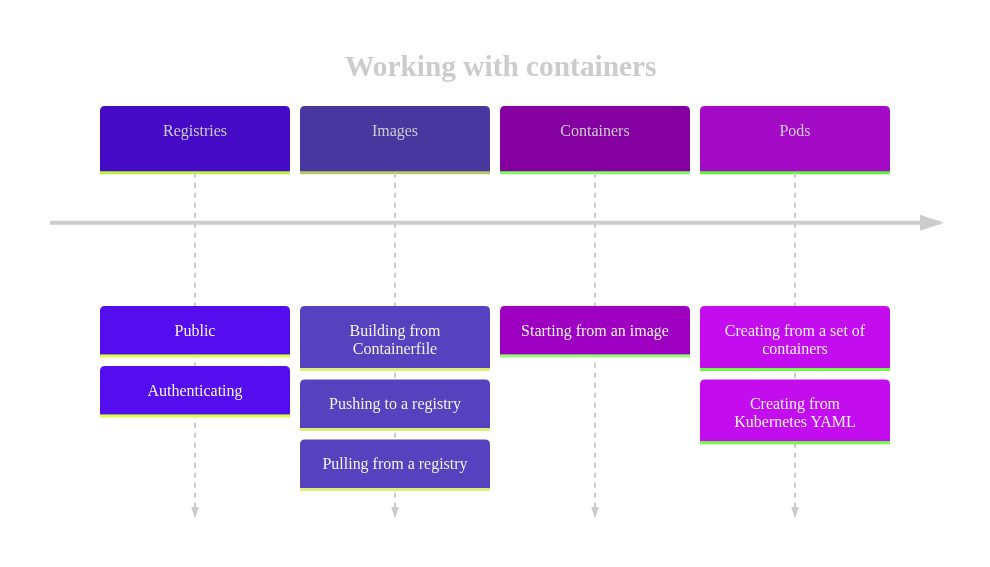
[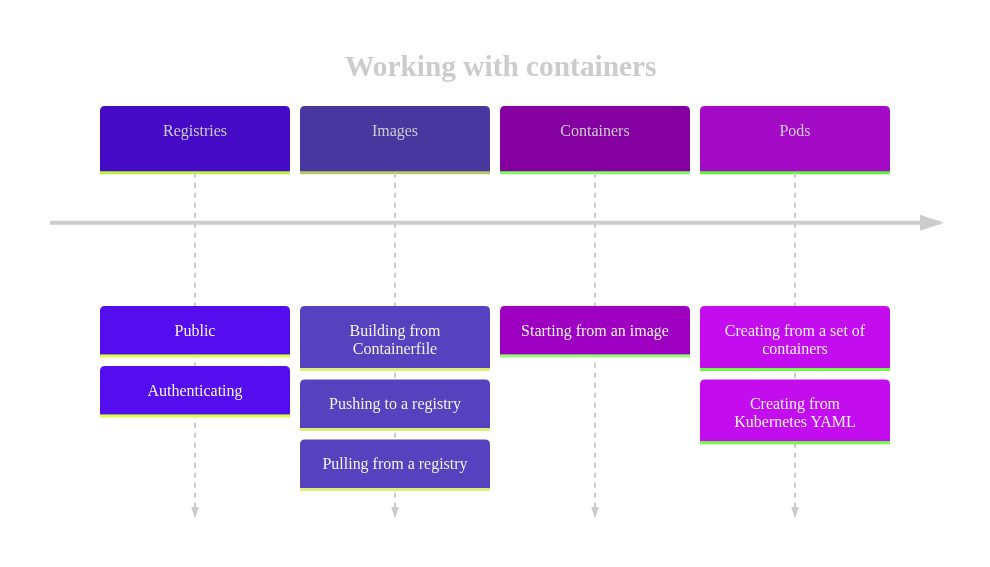](https://mermaid.live/edit#pako:eNptkt2OmzAQhV_FchVxw0ZAQvi5201VqequtOpWrVpxY_BArDV2ZA_t0ijvXgNNINLe4PGcb47HZk600hxoTlerU6EIEUpgTsaQEE_q5hF-g_Ry4nEou8bz_yt4gBaGdMks3Ga_MyNYKcF6VyMnHY1omen3Wmoz1H1Iy7iqd5fSmfgGbzhTVVUtEAuVVvzWpk5DvlkwCAbFDcKTKKzr92wetOFgZjIIggVWa4WfWCtkP4iWKXtnwYjam4jzsLjPebUqFIoWpFAwRCiB_NDmVaiG_BF4IO40ZE40tlBfoREWjQA7ueTkuSulqC67-849ojOpGLr6Qn1uWTOzD52QfPCtjW7J_uJbCwmznT0MBGrCiJlO62dRymv5Ut4vWpzQF2QGZ1YRMXRSqGfNr8zeAFswxAISXd_c9z3wS1eCUYBgyc_7p0fq0xZMywR3czhOTEHHSSpo7kL3o14L6t7ZcaxD_dKriuZoOvBpd-QM4aNgjWEtzWsmrcsCF6jN0zTY43z79MgUzU_0jeZ3m816k8RRHMfpNgl3qU97mm-y7TrI0iTepmmUhlF89ulfrZ1puA6SLA6iNNplWZJkyWj2a9SGLs7_AF26CAk)
|
||||
[](https://mermaid.live/edit#pako:eNptkt2OmzAQhV_FchVxw0ZAQvi5201VqequtOpWrVpxY_BArDV2ZA_t0ijvXgNNINLe4PGcb47HZk600hxoTlerU6EIEUpgTsaQEE_q5hF-g_Ry4nEou8bz_yt4gBaGdMks3Ga_MyNYKcF6VyMnHY1omen3Wmoz1H1Iy7iqd5fSmfgGbzhTVVUtEAuVVvzWpk5DvlkwCAbFDcKTKKzr92wetOFgZjIIggVWa4WfWCtkP4iWKXtnwYjam4jzsLjPebUqFIoWpFAwRCiB_NDmVaiG_BF4IO40ZE40tlBfoREWjQA7ueTkuSulqC67-849ojOpGLr6Qn1uWTOzD52QfPCtjW7J_uJbCwmznT0MBGrCiJlO62dRymv5Ut4vWpzQF2QGZ1YRMXRSqGfNr8zeAFswxAISXd_c9z3wS1eCUYBgyc_7p0fq0xZMywR3czhOTEHHSSpo7kL3o14L6t7ZcaxD_dKriuZoOvBpd-QM4aNgjWEtzWsmrcsCF6jN0zTY43z79MgUzU_0jeZ3m816k8RRHMfpNgl3qU97mm-y7TrI0iTepmmUhlF89ulfrZ1puA6SLA6iNNplWZJkyWj2a9SGLs7_AF26CAk)
|
||||
|
||||
1. [Work with registries](/docs/containers/registries).
|
||||
|
||||
|
|
|
|||
|
|
@ -36,7 +36,7 @@ When deactivating an extension, Podman Desktop will:
|
|||
|
||||
### Example boilerplate code
|
||||
|
||||
This is an example `extensions/foobar/src/extensions.ts` file with the basic `activate ` and `deactivate` functionality, provided that you already have a `package.json` created as well:
|
||||
This is an example `extensions/foobar/src/extensions.ts` file with the basic `activate` and `deactivate` functionality, provided that you already have a `package.json` created as well:
|
||||
|
||||
```ts
|
||||
import * as extensionApi from '@podman-desktop/api';
|
||||
|
|
@ -382,7 +382,7 @@ export default config;
|
|||
|
||||
1. To start Podman Desktop with your extension loaded, run the following from your clone of the Podman Desktop repo:
|
||||
|
||||
```
|
||||
```shell
|
||||
yarn watch --extension-folder /path/to/your/extension
|
||||
```
|
||||
|
||||
|
|
@ -481,7 +481,7 @@ export namespace foobar {
|
|||
}
|
||||
```
|
||||
|
||||
2. The `packages/main/src/plugin/extension-loader.ts` acts as an extension loader that defines all the actions needed by the API. Modify it to add the main functionality of `hello()` under the `foobar` namespace const:
|
||||
2. The `packages/main/src/plugin/extension-loader.ts` acts as an extension loader that defines all the actions needed by the API. Modify it to add the main functionality of `hello()` under the `foobar` namespace const: <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||
```ts
|
||||
// It's recommended you define a class that you retrieve from a separate file
|
||||
|
|
@ -517,7 +517,7 @@ return <typeof containerDesktopAPI>{
|
|||
};
|
||||
```
|
||||
|
||||
3. The above code won't work until we've created the class! So let's create a `packages/main/src/plugin/foobar-client.ts` file with the functionality:
|
||||
3. The above code won't work until we've created the class! So let's create a `packages/main/src/plugin/foobar-client.ts` file with the functionality: <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||
```ts
|
||||
export class FoobarClient {
|
||||
|
|
@ -527,7 +527,7 @@ export class FoobarClient {
|
|||
}
|
||||
```
|
||||
|
||||
4. An instance of this class needs to be created and passed to the constructor of the `ExtensionLoader`, in `packages/main/src/plugin/index.ts`:
|
||||
4. An instance of this class needs to be created and passed to the constructor of the `ExtensionLoader`, in `packages/main/src/plugin/index.ts`: <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||
```ts
|
||||
const foobarClient = new FoobarClient();
|
||||
|
|
@ -537,9 +537,9 @@ this.extensionLoader = new ExtensionLoader(
|
|||
);
|
||||
```
|
||||
|
||||
5. In package.json you can register some setting through the configuration settings property
|
||||
5. In package.json you can register some setting through the configuration settings property <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||
For example if you contribute a property named `podman.binary.path` it will display `Path` in Podman Desktop UI setting, and if you change it to `podman.binary.pathToBinary ` it becomes `Path To Binary` in the title.
|
||||
For example if you contribute a property named `podman.binary.path` it will display `Path` in Podman Desktop UI setting, and if you change it to `podman.binary.pathToBinary` it becomes `Path To Binary` in the title.
|
||||
|
||||
```ts
|
||||
|
||||
|
|
@ -555,7 +555,7 @@ For example if you contribute a property named `podman.binary.path` it will disp
|
|||
},
|
||||
```
|
||||
|
||||
6. Last step! Call the new API call to the extension you are implementing from your extension:
|
||||
6. Last step! Call the new API call to the extension you are implementing from your extension: <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||
```ts
|
||||
export async function activate(extensionContext: extensionApi.ExtensionContext): Promise<void> {
|
||||
|
|
|
|||
|
|
@ -338,7 +338,7 @@ When the `checkPodmanInstalled` step becomes active, the command `podman.onboard
|
|||
|
||||
You might wonder: who or what sets the context value? If you use a custom context value, it should be your extension's job to set it. Following the example above, we could set the context value during the execution of `podman.onboarding.checkPodmanInstalled` such as
|
||||
|
||||
```
|
||||
```js
|
||||
extensionApi.commands.registerCommand(
|
||||
'podman.onboarding.checkPodmanInstalled',
|
||||
async () => {
|
||||
|
|
@ -356,11 +356,11 @@ After updating the context, the UI is refreshed, and Podman Desktop moves the us
|
|||
|
||||
The **content** property is an array of arrays where each item in the parent array defines a row, and each item in the child arrays defines a cell.
|
||||
|
||||
```
|
||||
```js
|
||||
content = [
|
||||
["cell", "cell"], //row
|
||||
["cell", "cell", "cell"], //row
|
||||
]
|
||||
['cell', 'cell'], //row
|
||||
['cell', 'cell', 'cell'], //row
|
||||
];
|
||||
```
|
||||
|
||||
The JSON schema for a content cell entry is
|
||||
|
|
@ -467,7 +467,7 @@ Adding a complete list in the `package.json` can be confusing, so a better appro
|
|||
|
||||
at runtime, `${onboardingContext:warningsMarkdown}` is replaced by the actual list filled in the backend
|
||||
|
||||
```
|
||||
```js
|
||||
const warnings = [];
|
||||
...
|
||||
const warning = {
|
||||
|
|
|
|||
|
|
@ -31,7 +31,7 @@ Podman Desktop has a set of context keys that are evaluated to Boolean true/fals
|
|||
|
||||
| Context key | True when |
|
||||
| ----------------------------- | ---------------------------- |
|
||||
| **Operating system contexts** |
|
||||
| **Operating system contexts** | |
|
||||
| isLinux | True when the OS is Linux. |
|
||||
| isWindows | True when the OS is Windows. |
|
||||
| isMac | True when the OS is macOS. |
|
||||
|
|
@ -53,10 +53,10 @@ If omitted, the key/value is set globally. For this reason it is recommended to
|
|||
|
||||
The first example below sets the key `"podmanIsInstalled"` to true globally while the second example sets the key `"toolInstalled"` to `oc.exe` using the onboarding scope.
|
||||
|
||||
```
|
||||
extensionsAPI.context.setValue('podmanIsInstalled', true);
|
||||
```js
|
||||
extensionsAPI.context.setValue('podmanIsInstalled', true);
|
||||
|
||||
extensionsAPI.context.setValue('toolInstalled', 'oc.exe', 'onboarding');
|
||||
extensionsAPI.context.setValue('toolInstalled', 'oc.exe', 'onboarding');
|
||||
```
|
||||
|
||||
After setting the `toolInstalled` to `oc.exe`, you could use this information in the `when` clause to enable something
|
||||
|
|
|
|||
|
|
@ -12,17 +12,17 @@ Installing an extension is a great way to expand the capability of Podman Deskto
|
|||
|
||||
#### Procedure
|
||||
|
||||
1. Click on the **Extensions** button.
|
||||
1. Click on the **Extensions** button. <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||

|
||||

|
||||
|
||||
2. Browse the **Catalog** and install the extension.
|
||||
2. Browse the **Catalog** and install the extension. <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||

|
||||

|
||||
|
||||
3. Alternatively, you can also press **Install custom...** to install an extension from a container image.
|
||||
3. Alternatively, you can also press **Install custom...** to install an extension from a container image. <!-- markdownlint-disable-line MD029 -->
|
||||
|
||||

|
||||

|
||||
|
||||
#### Verification
|
||||
|
||||
|
|
|
|||
|
|
@ -51,6 +51,7 @@ Podman Desktop requires [Podman Engine](https://docs.podman.io/en/latest/index.h
|
|||
:::info[Prerequisite]
|
||||
|
||||
- [Homebrew](https://brew.sh/)
|
||||
|
||||
:::
|
||||
|
||||
### Installation steps
|
||||
|
|
|
|||
|
|
@ -27,7 +27,7 @@ You can create multiple local Kind-powered Kubernetes clusters.
|
|||
- **Provider Type**: `podman`
|
||||
- **HTTP Port**: `9090`
|
||||
- **HTTPS Port**: `9443`
|
||||
- **Setup an ingress controller (Contour https://projectcontour.io)**: Enabled
|
||||
- **Setup an ingress controller [Contour](https://projectcontour.io)**: Enabled
|
||||
- **Node’s container image (Available image tags on [kind/releases](https://github.com/kubernetes-sigs/kind/releases))**: Left empty to use latest.
|
||||
|
||||
1. (Optionally) Click the **Show logs** button to display the logs.
|
||||
|
|
|
|||
|
|
@ -28,7 +28,7 @@ With Podman Desktop, you can push an image to your local Kind-powered Kubernetes
|
|||
|
||||
With recent versions of Kind, the `crictl` command can be used - e.g., `podman exec -it kind-cluster-control-plane crictl images`. The name of the control plane container may vary, so you can use a filter to query for the container:
|
||||
|
||||
```
|
||||
```shell
|
||||
podman exec -it $(podman ps --filter "label=io.x-k8s.kind.role=control-plane" --format {{.Names}}) crictl images
|
||||
```
|
||||
|
||||
|
|
|
|||
|
|
@ -26,13 +26,13 @@ Consider using the `DOCKER_HOST` environment variable to migrate transparently f
|
|||
<Tabs groupId="operating-systems">
|
||||
<TabItem value="win" label="Windows">
|
||||
|
||||
1. Identify the location of your Podman pipe
|
||||
1. Identify the location of your Podman pipe <!-- markdownlint-disable MD029 -->
|
||||
|
||||
```shell-session
|
||||
$ podman machine inspect --format '{{.ConnectionInfo.PodmanPipe.Path}}'
|
||||
```
|
||||
|
||||
2. Set the `DOCKER_HOST` environment variable to your Podman pipe location. You'll need to replace back slashes with forward slashes and add the `npipe://` scheme to the path retrieved previously:
|
||||
2. Set the `DOCKER_HOST` environment variable to your Podman pipe location. You'll need to replace back slashes with forward slashes and add the `npipe://` scheme to the path retrieved previously: <!-- markdownlint-disable MD029 -->
|
||||
|
||||
> Example:
|
||||
>
|
||||
|
|
|
|||
|
|
@ -212,7 +212,7 @@ Podman Desktop might then reconnect in rootless mode, and fail to display the im
|
|||
|
||||
When running the Podman provider, a warning shows regarding Docker compatibility mode on the dashboard:
|
||||
|
||||
```
|
||||
```<!-- markdownlint-disable MD040 -->
|
||||
⚠️ Docker Socket Compatibility: Podman is not emulating the default Docker socket path: '/var/run/docker.sock'. Docker-specific tools may not work. See troubleshooting page on podman-desktop.io for more information.
|
||||
```
|
||||
|
||||
|
|
|
|||
Loading…
Reference in a new issue